With no exceptions, all material on this site is presented for free, made available for educational purposes.
Articles by category
Click on the link to only display articles related to each category. Some articles are address multiple categories.
- Computer security (24)
- Payment cards (2)
- Technology & business (31)
- WordPress (13)
Latest articles
Click one of the links above for all articles
- Enable Zip Archive for Duplicator in HostMantis
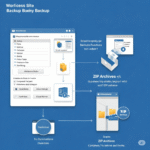 Are you using a utility that requires Zip Archive Enabled in WordPress? For me, this was the backup utility Duplicator. And there’s the pain point. This took quite a bit longer to find than I expected! Here’s the journey to success. 1. The Issue The issue arose because… Read more: Enable Zip Archive for Duplicator in HostMantis
Are you using a utility that requires Zip Archive Enabled in WordPress? For me, this was the backup utility Duplicator. And there’s the pain point. This took quite a bit longer to find than I expected! Here’s the journey to success. 1. The Issue The issue arose because… Read more: Enable Zip Archive for Duplicator in HostMantis - HostMantis Review: Seriously Good and Reliable Web Hosting!
 Diving into the world of web hosting can feel like navigating a complex network, a bit like the physical landscapes of wilderness paths and waterfalls I often hike. I’m searching for that stable, secure hosting company that not only keeps my online presence running smoothly and sets up… Read more: HostMantis Review: Seriously Good and Reliable Web Hosting!
Diving into the world of web hosting can feel like navigating a complex network, a bit like the physical landscapes of wilderness paths and waterfalls I often hike. I’m searching for that stable, secure hosting company that not only keeps my online presence running smoothly and sets up… Read more: HostMantis Review: Seriously Good and Reliable Web Hosting! - Medical Device Cyber Security: Challenges, Guidance, and Best Practices for Secure Deployment
 Last update: 2023-08-04 1. Background Cyberattacks on medical devices are a growing threat to patient safety. Cybersecurity threats to healthcare have increased in both frequency and severity, and continue to be clinically impactful causing healthcare delays. The security of medical devices is essential to protect patient safety and… Read more: Medical Device Cyber Security: Challenges, Guidance, and Best Practices for Secure Deployment
Last update: 2023-08-04 1. Background Cyberattacks on medical devices are a growing threat to patient safety. Cybersecurity threats to healthcare have increased in both frequency and severity, and continue to be clinically impactful causing healthcare delays. The security of medical devices is essential to protect patient safety and… Read more: Medical Device Cyber Security: Challenges, Guidance, and Best Practices for Secure Deployment - How to secure FDA approved medical devices from hackers
 Medical devices present a unique cyber challenge for hospitals. Read these guidelines before deploying them to the hospital enterprise network
Medical devices present a unique cyber challenge for hospitals. Read these guidelines before deploying them to the hospital enterprise network - Python paradise: Ditch the setup, soar with cloud Python
 Are you an experienced Python programmer? Then this article is absolutely for you. On the other hand, if you are a new Python programmer, or new to programming? Then this article is DEFINITELY for you! Click here to Google Colab Table of contents Colab: Your browser-Based Python Playground… Read more: Python paradise: Ditch the setup, soar with cloud Python
Are you an experienced Python programmer? Then this article is absolutely for you. On the other hand, if you are a new Python programmer, or new to programming? Then this article is DEFINITELY for you! Click here to Google Colab Table of contents Colab: Your browser-Based Python Playground… Read more: Python paradise: Ditch the setup, soar with cloud Python - “Hello can you hear me”: Social engineering or part of the call?
 Have you ever received a phone call where the caller’s first question is, “Can you hear me?” It is not likely what you’ve been told,
Have you ever received a phone call where the caller’s first question is, “Can you hear me?” It is not likely what you’ve been told, - Watering Hole attack: Cybercriminals subvert your most vulnerable favorite websites
 A watering hole attack is a type of cyberattack in which the attacker targets a website or online service that is known to be frequented by the victim’s target audience. The attacker then compromises the website or service and injects malicious code into it. When the victim visits the website or uses the service, they are infected with malware.
A watering hole attack is a type of cyberattack in which the attacker targets a website or online service that is known to be frequented by the victim’s target audience. The attacker then compromises the website or service and injects malicious code into it. When the victim visits the website or uses the service, they are infected with malware. - The best free video editors for vlogging, YouTube, and more!
 Are you searching for a video editor? If so, this page is for you! OpenShot Video Editor, Kdenlive, YouTube Video Maker…
Are you searching for a video editor? If so, this page is for you! OpenShot Video Editor, Kdenlive, YouTube Video Maker… - HostMantis WordPress web hosting review – Excellent A1!
 This is a review of HostMantis, a web hosting company that has been providing reliable and affordable hosting services since 2014. They offer a range of hosting solutions, including shared hosting, reseller hosting, VPS hosting, and dedicated servers.
This is a review of HostMantis, a web hosting company that has been providing reliable and affordable hosting services since 2014. They offer a range of hosting solutions, including shared hosting, reseller hosting, VPS hosting, and dedicated servers. - Unveiling the Top Free Internet Faxing Providers
 Free internet fax options allow you to send and receive faxes over the internet without the need for a fax machine or a dedicated phone line. These services are often referred to as “online fax services” or “virtual fax services.”
Free internet fax options allow you to send and receive faxes over the internet without the need for a fax machine or a dedicated phone line. These services are often referred to as “online fax services” or “virtual fax services.” - Unmasking The Future Of Malware with ChatGPT: A Comprehensive Analysis And Expert Commentary On The Evolving Threat Landscape
 “The future of malware” is a trigger for most of us in computer security. Most cyber professionals have an idea of what they think malware looks like in the next few years, but truly few of us write about it or document it in a formal way. In… Read more: Unmasking The Future Of Malware with ChatGPT: A Comprehensive Analysis And Expert Commentary On The Evolving Threat Landscape
“The future of malware” is a trigger for most of us in computer security. Most cyber professionals have an idea of what they think malware looks like in the next few years, but truly few of us write about it or document it in a formal way. In… Read more: Unmasking The Future Of Malware with ChatGPT: A Comprehensive Analysis And Expert Commentary On The Evolving Threat Landscape - Reviving Your Website: Dead Link Checkers for Seamless Online Experiences
 The user experience is paramount to revisits. Dead links are frustrating for users, and reduces that “first” (or second!)_ impression. This article provides a few dead link checkers to validate a site’s internal and outbound links.
The user experience is paramount to revisits. Dead links are frustrating for users, and reduces that “first” (or second!)_ impression. This article provides a few dead link checkers to validate a site’s internal and outbound links. - Breaking the glass: Mastering BreakGlass Techniques for Emergency Access
 Breakglass access is a required component of business recovery. It should only be used in emergency situations.
Breakglass access is a required component of business recovery. It should only be used in emergency situations. - Link Tracking: Unveiling the best Tracker websites with enhanced analytics
 Looking to track who clicked your links, and when? This article will help with link tracking!
Looking to track who clicked your links, and when? This article will help with link tracking! - Where to find “free use licensed” photos and videos
 Finding the perfect photos and images is always a chore. Finding the perfect “freely licensed” image is a double chore! This article is here to help you.
Finding the perfect photos and images is always a chore. Finding the perfect “freely licensed” image is a double chore! This article is here to help you. - Enhancing Security: Protecting Networks with Outbound Firewall Rules
 Reconfiguring firewalls in operational environments potentially breaks things. This article helps to develop a plan for implementing change.
Reconfiguring firewalls in operational environments potentially breaks things. This article helps to develop a plan for implementing change. - LinkedIn Mastery: Elevate Your Career with Proven Strategies for Success
 Getting started in LinkedIn is intimidating. That’s okay! This article is going to help you persuasively approach LinkedIn.
Getting started in LinkedIn is intimidating. That’s okay! This article is going to help you persuasively approach LinkedIn. - Safeguarding your domain search: how to avoid ‘front runners’
 Have you every had that perfect domain name, searched online, found it was available… only to have it taken away in the couple of days it took you to decide to buy? That’s the thievery of front runners. This article is for you!
Have you every had that perfect domain name, searched online, found it was available… only to have it taken away in the couple of days it took you to decide to buy? That’s the thievery of front runners. This article is for you! - Coronavirus special report: Separating your Work and Personal identities
 We are our identity. Whether working from home or working in an office, separating your “Work Identity” and “Personal Identity” remains very important, both for your protection and for the security of your company. Read this article for more information.
We are our identity. Whether working from home or working in an office, separating your “Work Identity” and “Personal Identity” remains very important, both for your protection and for the security of your company. Read this article for more information. - The first rule of security: “Be aware” of your surroundings
 How can you protect yourself on the internet? The same methods you use to keep you safe “in real life” will also keep you safe in the digital world. First thing? Be aware of your surroundings.
How can you protect yourself on the internet? The same methods you use to keep you safe “in real life” will also keep you safe in the digital world. First thing? Be aware of your surroundings. - Vishing Scams: How to Safeguard Yourself from Deceptive Voice Attacks
 The vish: Vishing and social engineering are nefarious confidence scams that pretend to be helping you. This article will help you avoid being a victim.
The vish: Vishing and social engineering are nefarious confidence scams that pretend to be helping you. This article will help you avoid being a victim. - Protecting Your Personal Privacy at Work: Tips for Confidentiality and Security
 In today’s world of privacy, you might be surprised that your company is recording every one of your keystrokes. Keep your private information private.
In today’s world of privacy, you might be surprised that your company is recording every one of your keystrokes. Keep your private information private. - The Ups and Downs: Exploring the Journey of InMotion Hosting – A Revealing Two-Year Review
 This article presents a candid review of inmotion hosting, focused on both “reseller” and “end user” accounts: Ease of use, setup, speed, and configuration.
This article presents a candid review of inmotion hosting, focused on both “reseller” and “end user” accounts: Ease of use, setup, speed, and configuration. - Defending Your Wallet: Unveiling the Thrilling World of Payment Card Theft and How to Stay Safe
 Seems every day there are new reports of payment and credit card theft. Explore how payment card theft happens, and how to protect yourself.
Seems every day there are new reports of payment and credit card theft. Explore how payment card theft happens, and how to protect yourself. - Bulletproof Your Website: Enhancing WordPress Security with File System Protection for Login
 WordPress login hardening is a great step towards security. This article explains adding an additional password to the wp-login.php file. Every user will have to enter a secondary password before retrieving wp-login.
WordPress login hardening is a great step towards security. This article explains adding an additional password to the wp-login.php file. Every user will have to enter a secondary password before retrieving wp-login. - Domain Dilemma: The Pitfalls of Free Domains and the Benefits of Owning Your Own
 Ready to show off a new domain? Want to use a “personalized” domain for a new customer, but don’t wish to buy the domain until the customer actually engages you with a contract? Sometimes having a free domain is of benefit.
Ready to show off a new domain? Want to use a “personalized” domain for a new customer, but don’t wish to buy the domain until the customer actually engages you with a contract? Sometimes having a free domain is of benefit. - Brighten Your Website: How to Remove the Default Featured Image Shading in WordPress 2019 Theme
 This article is going to help you change the built in WordPress 2019 Gutenberg Featured Image shading.
This article is going to help you change the built in WordPress 2019 Gutenberg Featured Image shading. - Computer Security Incident Response (NIST SP800-61r2)
 The NIST Computer Security Incident Handling Guide provides a framework for creating a company focused computer security incident response plan.
The NIST Computer Security Incident Handling Guide provides a framework for creating a company focused computer security incident response plan. - Data Breaches Unmasked: The Devastating Reality of Identity Theft
 Identity theft is terrifying. This short article will explore what you can do if your information is compromised, and give you advice even if it hasn’t (yet).
Identity theft is terrifying. This short article will explore what you can do if your information is compromised, and give you advice even if it hasn’t (yet). - Phish for phun and profit
 Phishing is a real problem, and that problem is only increasing in frequency. Phish attacks come in many different forms. Everyone is affected by phishing. Whether it be that a credit card number is stolen from your family member, or your friend gets their Facebook account hijacked, or… Read more: Phish for phun and profit
Phishing is a real problem, and that problem is only increasing in frequency. Phish attacks come in many different forms. Everyone is affected by phishing. Whether it be that a credit card number is stolen from your family member, or your friend gets their Facebook account hijacked, or… Read more: Phish for phun and profit - WordPress Plugins – 2.1 Mail Relay
 Let me ask an honest question. Would you rather be doing business with “bobrx153@hotmail.com” or “bob@randolf.com” ? Which one looks more professional? Which one looks more trustworthy?
Let me ask an honest question. Would you rather be doing business with “bobrx153@hotmail.com” or “bob@randolf.com” ? Which one looks more professional? Which one looks more trustworthy? - WordPress Plugins (1.0 Introduction)
 WordPress is an incredible Content Management System — and it is free! WordPress off the shelf is just that — a content management system. The best part of WordPress is that it is extensible.
WordPress is an incredible Content Management System — and it is free! WordPress off the shelf is just that — a content management system. The best part of WordPress is that it is extensible. - WordPress Plugins (2.0 Security: Confidentiality, Integrity, Availability)
 This post is a part of the WordPress Plugins discussion threads and focuses on Plugins that increase the Security of your WordPress site. Just as with all WordPress Plugin recommendations, only “free” Plugins will be considered. Security First, a definition for this very important section. Security is protecting… Read more: WordPress Plugins (2.0 Security: Confidentiality, Integrity, Availability)
This post is a part of the WordPress Plugins discussion threads and focuses on Plugins that increase the Security of your WordPress site. Just as with all WordPress Plugin recommendations, only “free” Plugins will be considered. Security First, a definition for this very important section. Security is protecting… Read more: WordPress Plugins (2.0 Security: Confidentiality, Integrity, Availability) - WordPress Plugins – 2.1 Interact with your users – Mailjet Outbound mail relay
 Emails are integratl to business. Whether for transacitional email to change a user password, or as marketing campain, this Mailjet configurator is for you.
Emails are integratl to business. Whether for transacitional email to change a user password, or as marketing campain, this Mailjet configurator is for you. - WordPress Post Revisions
 Have you worked hard on a post, only to forget to save the post? I have. If you are looking to “autosave” your WordPress posts, this post is for you!
Have you worked hard on a post, only to forget to save the post? I have. If you are looking to “autosave” your WordPress posts, this post is for you! - Using Artificial Intelligence to create predictive systems
 The term Artificial Intelligence (or AI) was coined in the mid 1950s. AI technology was heavily funded by the Department of Defense for many years. Unfortunately, the practitioners at the time were overly optimistic and failed to overcome some of the difficulties that they faced. By the mid… Read more: Using Artificial Intelligence to create predictive systems
The term Artificial Intelligence (or AI) was coined in the mid 1950s. AI technology was heavily funded by the Department of Defense for many years. Unfortunately, the practitioners at the time were overly optimistic and failed to overcome some of the difficulties that they faced. By the mid… Read more: Using Artificial Intelligence to create predictive systems - Strategic breakthrough: Unleashing the power of Business & Technology Planning for unstoppable success
 This article explores basic ideas that you should keep in mind as you are starting or continuing your business. It is intended to provoke deeper thoughts for you and your executive team. From business continuity, to free coffee and free WiFi, we’ll look into ideas that are important to businesses… and to customers.
This article explores basic ideas that you should keep in mind as you are starting or continuing your business. It is intended to provoke deeper thoughts for you and your executive team. From business continuity, to free coffee and free WiFi, we’ll look into ideas that are important to businesses… and to customers. - Exploring advantages and disadvantages of Cloud: IAAS PAAS SAAS
 Cloud early, cloud often: Four words to say that now is the time to embrace cloud services. Read more to understand and explore the advantages and disadvantages of “cloud” solutions.
Cloud early, cloud often: Four words to say that now is the time to embrace cloud services. Read more to understand and explore the advantages and disadvantages of “cloud” solutions. - Exploiting the SDLC: Unleashing the Devastating Power of Cyber Warfare
 Attacking software is really attacking the software development process. The adversary is looking to take advantage of software defects before those defects are repaired. This paper explores the attack timeline in the SDLC
Attacking software is really attacking the software development process. The adversary is looking to take advantage of software defects before those defects are repaired. This paper explores the attack timeline in the SDLC - My site is blocked! Unlock URL access with content filtering companies
 Content filtering categorize domains based on reputation. Many companies block domains based on those filters. This article will show you how to register your domains so that they are not inadvertently blocked.
Content filtering categorize domains based on reputation. Many companies block domains based on those filters. This article will show you how to register your domains so that they are not inadvertently blocked. - WordPress: Transform Your Experience with Subdirectories
 Using subdirectories just makes things cleaner. This article will help you add https, www, and run WordPress from a subdirectory.
Using subdirectories just makes things cleaner. This article will help you add https, www, and run WordPress from a subdirectory. - Identity theft
 Our online identity IS our identity. Someone masquerading as you is potentially a dangerous situation, but it is at least creepy. The problem is, as sure as everyone will pay taxes this year, we will all have our online identity compromised. What do you tell your colleagues who have had their identity stolen? What do you tell your family who have not *yet* had their identity stolen? What should they do? And what should they have done in order to reduce the vulnerability? This paper will give you ideas on preventing problems in online identity theft, and also provide guidance on how to fix a problem if it happens.
Our online identity IS our identity. Someone masquerading as you is potentially a dangerous situation, but it is at least creepy. The problem is, as sure as everyone will pay taxes this year, we will all have our online identity compromised. What do you tell your colleagues who have had their identity stolen? What do you tell your family who have not *yet* had their identity stolen? What should they do? And what should they have done in order to reduce the vulnerability? This paper will give you ideas on preventing problems in online identity theft, and also provide guidance on how to fix a problem if it happens. - Centrally managing WordPress sites
 Managing multiple WordPress sites is no easy task. While managing a single WordPress site in itself can seem difficult at times, managing many WordPress sites concurrently requires keeping track of multiple security updates, different Plug-In updates, Theme updates, backups, usernames and credentials, and Firewall settings. Fortunately, this is… Read more: Centrally managing WordPress sites
Managing multiple WordPress sites is no easy task. While managing a single WordPress site in itself can seem difficult at times, managing many WordPress sites concurrently requires keeping track of multiple security updates, different Plug-In updates, Theme updates, backups, usernames and credentials, and Firewall settings. Fortunately, this is… Read more: Centrally managing WordPress sites - Zero day, 0day, ohday, oh my!
 Hackers have a few things in their favor when it comes to getting into your network and stealing data. One of those things is the elusive zero day. When it comes to hacking, a zero day is an “exploitation against a publicly unknown vulnerability”. But hackers don’t need… Read more: Zero day, 0day, ohday, oh my!
Hackers have a few things in their favor when it comes to getting into your network and stealing data. One of those things is the elusive zero day. When it comes to hacking, a zero day is an “exploitation against a publicly unknown vulnerability”. But hackers don’t need… Read more: Zero day, 0day, ohday, oh my! - The end of the (land) line
 So you’ve looked at your local phone bill and it was… oh my, I’m paying that much for a simple landline phone number? This doesn’t seem right! How can I be paying $40 a month for a landline phone (base price around $15/month, plus “options” price like call… Read more: The end of the (land) line
So you’ve looked at your local phone bill and it was… oh my, I’m paying that much for a simple landline phone number? This doesn’t seem right! How can I be paying $40 a month for a landline phone (base price around $15/month, plus “options” price like call… Read more: The end of the (land) line - Business Continuity Planning
 Business Continuity Planning (BCP) is the pre-planning effort put in to make sure your business continues to operate even during adverse situations. BCP is the work put in before those imperfect days, in order to smoothly transition between “normal” operations and “backup” operations. A backhoe digs through the… Read more: Business Continuity Planning
Business Continuity Planning (BCP) is the pre-planning effort put in to make sure your business continues to operate even during adverse situations. BCP is the work put in before those imperfect days, in order to smoothly transition between “normal” operations and “backup” operations. A backhoe digs through the… Read more: Business Continuity Planning - Risk management – developing a framework
 Risk management is an essential skill for any business professional. Whether it be having a second screwdriver available on the job in case one is lost or broken, or it be having Errors and Omissions or liability insurance, we are constantly evaluating risks and the costs associated with… Read more: Risk management – developing a framework
Risk management is an essential skill for any business professional. Whether it be having a second screwdriver available on the job in case one is lost or broken, or it be having Errors and Omissions or liability insurance, we are constantly evaluating risks and the costs associated with… Read more: Risk management – developing a framework - Computer security hardening – safeguarding your systems
 Computer Security. Kind of scary, actually. With the likes of Target going down to hackers in late 2013, and a large attack on Home Depot in 2014, what can the rest of us do? If Home Depot can be compromised, how can I protect myself? The bad news —… Read more: Computer security hardening – safeguarding your systems
Computer Security. Kind of scary, actually. With the likes of Target going down to hackers in late 2013, and a large attack on Home Depot in 2014, what can the rest of us do? If Home Depot can be compromised, how can I protect myself? The bad news —… Read more: Computer security hardening – safeguarding your systems
